If you're here then your business might be focused on security awareness this year. Bravo! You're one of the smart ones.
Businesses must start to take cybersecurity risks from a social media threat more seriously and update their social media security approach moving into 2025.
It is no longer effective simply to have a firewall and antivirus or malware prevention software installed, and to hope for the best. Given that 1 in 3 businesses have experienced a data breach in the past year, it is important for organizations to act as quickly as possible and make upgrades to their security.
Login to any news outlet and you will see news of a data breach attack that took place recently. If that isn't concerning enough, sensitive data about your business and a phishing attack on your personal information can send you or your team into a spiral. So, it's great to focus on minimizing your cybersecurity risk as soon as possible.
One key area that has been increasingly exploited in recent years is that of business social media accounts. Social media is a massive business and a huge part of almost every business’ marketing strategy. We want to point out though, not taking close enough care around security risks of a chosen social media platform can lead to serious challenges.
In this article, we will dive into understanding the cybersecurity environment on social media specific to a business and 5 tips to make sure you are minimizing that risk.
Let's get right into it.
Understand the risks
There are a number of cyber risk areas relating to social media, many of which businesses won’t even realize can be so damaging.
Phishing attacks
We are used to seeing cyber attack phishing attacks in our emails, but phishing via social media is becoming all the more common. Some attacks are focused on data, while others will be directly relating to money and attempting to trick staff into making unnecessary payments.
Weak passwords
It is unfortunately still the case that many staff social media accounts use weak passwords. Sometimes these accounts are perceived to be a lower risk, and therefore users believe they don’t need to have a strong password.
Unmonitored accounts
Just like we saw in our post on social media for accountants, cyber criminals often target unmonitored social media accounts. This could be those of defunct campaigns, former employees, or any account that was once used for company social media but is no longer.
Human error

Human error is reported to be a major factor in 95% of all cyber breaches. Of course, everyone makes mistakes, but when these mistakes have a huge impact on cybersecurity, it is an issue that needs to be addressed. Mistakes often arise because employees don’t realize that they are doing something wrong in the first place.
Social media shadow IT
There are many pieces of software that can make business social media easier to manage. But it is vital to understand the risk of shadow IT, and how using unapproved applications can lead to cybersecurity risks. Shadow IT refers to any software that has not been approved by the IT team. The reason this can be a security risk is if the software is not up-to-date or contains known vulnerabilities, cybercriminals can exploit it.
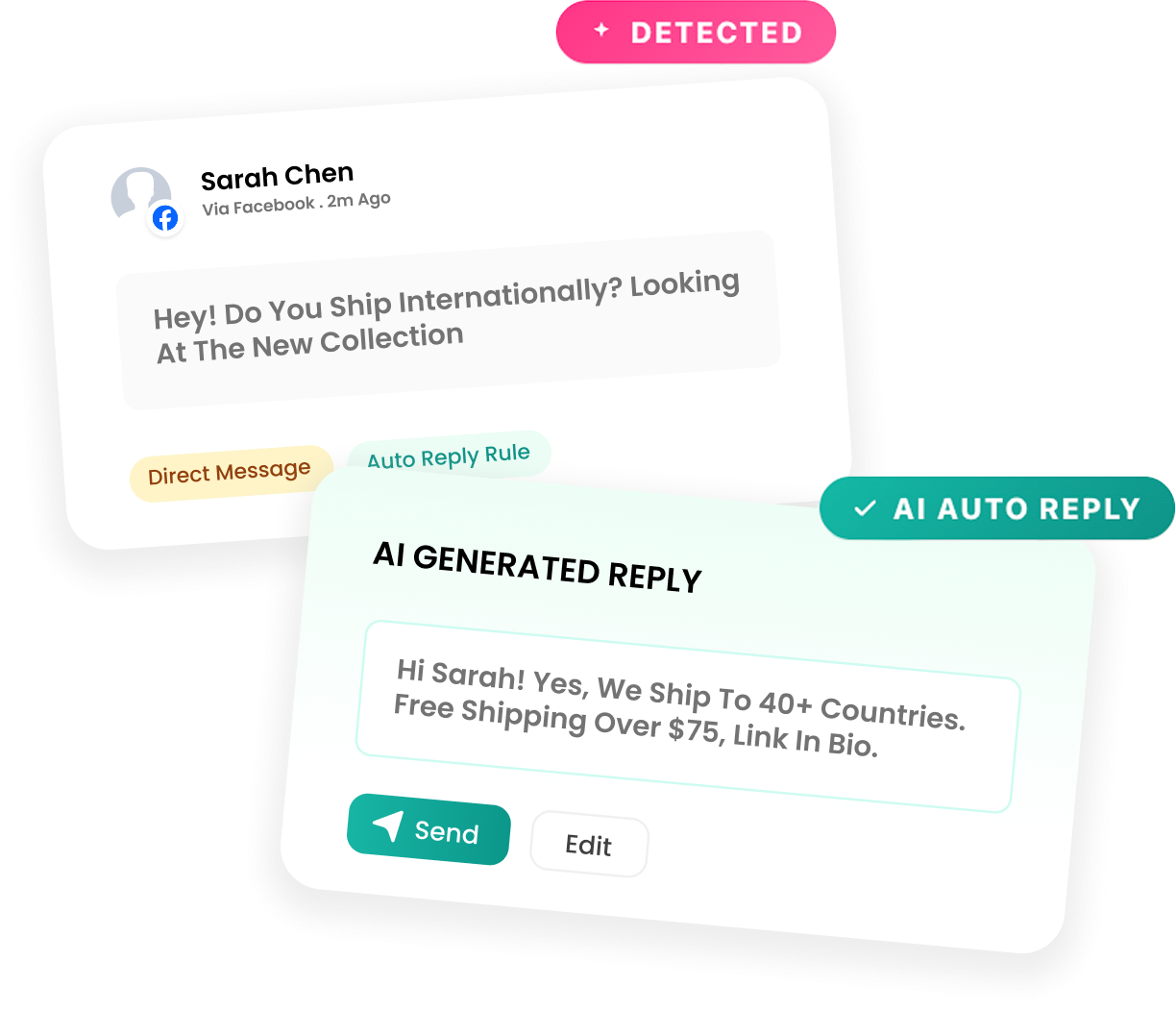
Social media management software companies like Eclincher take extra steps to secure sensitive information for their users privacy since they serve an international audience. They require captcha and other authentication strategies to ensure the safety of their clients information, require token renewal of personal social media accounts that are connected to the software among other strategies. Social media companies have a duty to protect sensitive information. Make sure your company covers their policies here before you invest in a new social media management tool.
Rising levels of social media oriented cybercrime
These risks unfortunately are leading to a very real spike in cybercrime through social media platforms. In fact, statistics suggest that cybercriminals extort close to $3.25 billion every year by exploiting social media channels. These are challenges that businesses face each and every day.
The fact is that some organizations have been too slow to adapt, and this has potentially left them vulnerable.
Changing your approach to cybersecurity
Businesses must start to take cybersecurity more seriously and update their approach. It is no longer effective simply to have a firewall and antivirus software installed, and to hope for the best.
These types of tools are still important, but they must be combined with both proactive and reactive tactics.
Minimizing and mitigating risk

Thankfully there are plenty of steps that you can take that will help you minimize and mitigate cybersecurity risk from social media.
Employee training
It is essential that employees are provided with appropriate training. Staff need to know how to protect themselves when using social media. High quality training can alert workers to the risks and give them advice and guidance on how to deal with problems as they arise. Training needs to be up-to-date and constantly refreshed - but we will talk more about that later.
Outsource your cybersecurity
The cybersecurity skills gap has made it prohibitively expensive to hire skilled professionals for most small and medium sized businesses. But that doesn’t mean you have to go without the kind of expertise needed. It can be a great idea to work with a company that offers cybersecurity services and outsource to them.
“As cybercrime becomes ever more complex and sophisticated, it is impossible for in-house SecOps teams to harness a high enough level of expertise to sufficiently shore up their company’s defenses,” says Rick Jones at Info Security Magazine “outsourcing cybersecurity not only seems like a smart decision for businesses, but it may also become an essential consideration in an environment lacking cyber-skills, but saturated with cybercrime”.
Multi-factor authentication
There is an extremely easy fix that almost all organizations could easily apply to all of their social media accounts in order to step up their security. Multi-factor authentication (MFA) is offered by all major social media platforms. It functionally asks for a second form of credentials when you attempt to log-in to your account.

“As a penetration tester, a major issue that I see regularly is a failure by organizations to enforce multi-factor authentication across systems and applications,” says Jed Kafetz, Head of Penetration Testing at Redscan. “Multi factor authentication provides an important secondary layer of defence in the event of a password being stolen and is especially important given people’s tendency to reuse passwords across accounts. If adopted more widely, I can confidently say that there would be far fewer security breaches.”
There are many different options in terms of authenticating credentials. A passcode could be sent to a mobile device, a different passcode could be entered, or biometric data could be verified.
Gather intelligence
Intelligence gathering is an important part of putting proper defences in place against cybercrime. Being prepared for cyber-crime is often the best way to defend against it. This returns to the issue of providing training that is relevant and up-to-date. You need to ensure that staff are informed on all the right challenges.
There are both paid and free threat intelligence tools so there is no excuse for your cybersecurity training to be underprepared. Prioritize with the tool that best meets the needs of your business and make plan for implementation.
Create a business social media policy
It is definitely important for your business to put a social media policy in place. This policy is a list of guidelines for how your business and employees should use social media for work. Having a company social media policy is not only a good idea from a cybersecurity perspective, it can also help to minimize bad PR and legal issues as well.
Your social media should cover issues around copyright, confidentiality and brand guidelines. However, it can also put in place expectations such as the devices that should be used for social media and information on avoiding common traps (such as quizzes that ask for personal details as these can be an identity theft risk).
Frequently Asked Questions
What is social media cybersecurity?
Social media cybersecurity is the practice of protecting your online accounts and personal information from being stolen or used by hackers. This can include using strong passwords, two-factor authentication, and privacy settings to help keep your data safe. It's important to be vigilant about cybercrime, especially as social media becomes an increasingly popular target for scammers and identity thieves
What are the top 5 security threats of social media?
The most common social media security threats include:
1) Malware and viruses that can be spread through social media links or attachments.
2) Phishing scams that use social media to extract personal information like passwords or credit card numbers.
3) Impersonation accounts that are used to scam people or spread malicious content.
4) Harassment and cyberbullying that can take place on social media platforms.
5) Data theft and unauthorized access to personal information that can be stored on social media networks.
How has social media impacted cyber security?
Social media has had a significant impact on cyber security in a number of ways. First, social media has created new opportunities for attackers to launch attacks. For example, attackers can use social media to spread malicious links or malware. Social media has only been around for a decade or so.
What are the common cyber-attacks in social media?
Email phishing is one of the most common cyber-attacks in social media. In email phishing, an attacker sends an email to a victim pretending to be from a legitimate organization, such as a bank or healthcare provider. The email usually contains a link that directs the victim to a website where they are asked to enter their username and password. Companies often spend time training their employees to be very cautious of the links and emails they click on.
Social media risk can be managed
Social media marketing can present cybersecurity risks. Don't let that scare you, but empower your business to be in the know, stay in the know with best business practices in this industry, and choosing partners and vendors that you trust. Being less reactive by taking a proactive approach allows you to minimize the potential danger from cyber threats. Companies must do as much as they can, as social media-related cybercrime is only likely to rise in the future.

.svg)
.svg)
.svg)

.svg)
.svg)
.svg)

.svg)

.svg)
.svg)

.svg)





.svg)
.svg)
.svg)
.svg)

.svg)




.png)
%20(1).png)
.png)





.svg)
.svg)
.svg)

.png)
.png)
.png)
.svg)
.svg)
%20(1).png)
.svg)
.png)


.png)
.svg)
.svg)
.svg)
%20(1).png)
.png)
.png)

.png)
.png)
.svg)
.svg)
%20(1).png)
%20(1).png)
.png)



.png)




